Internal Network Assessment
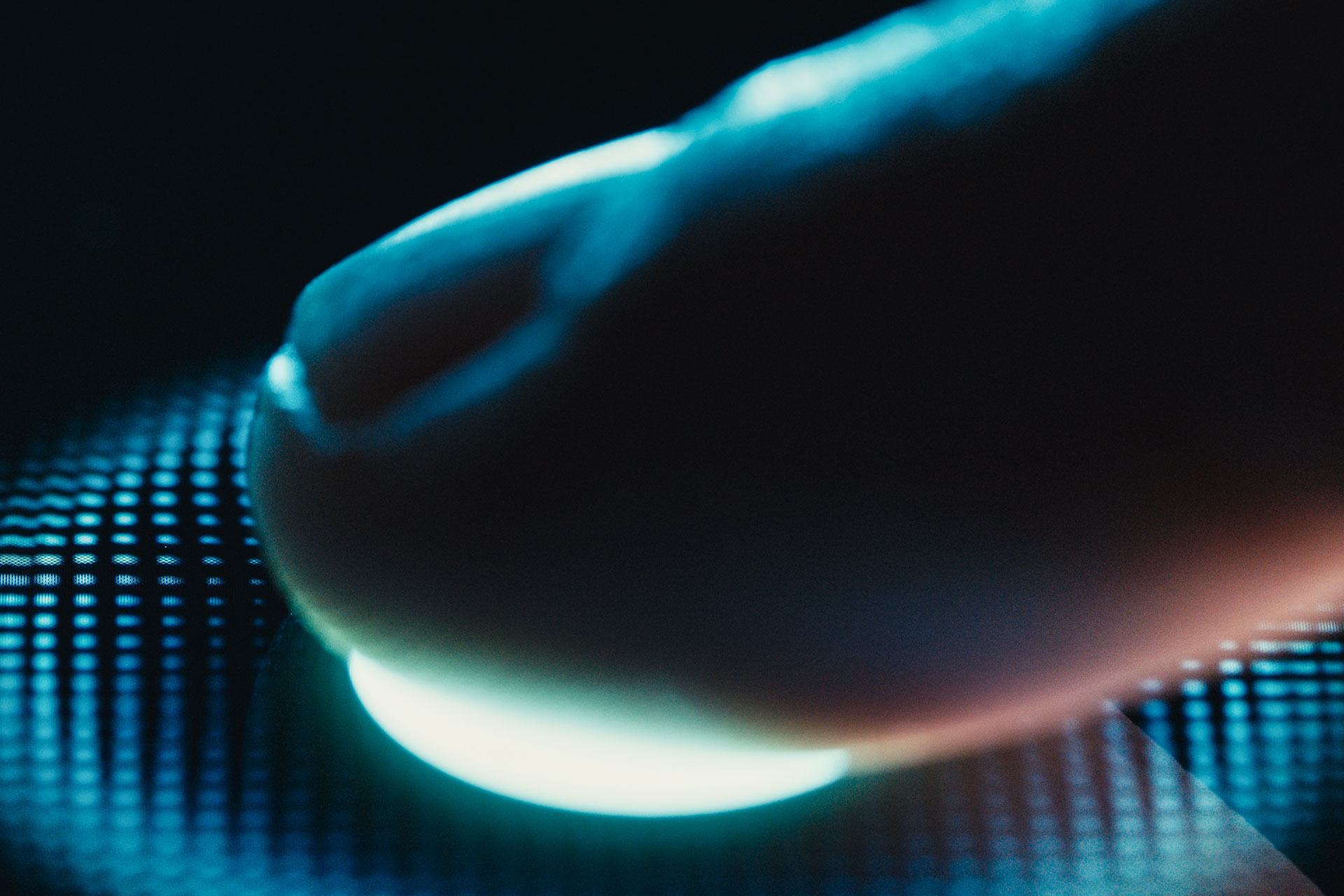
Strafe Cybersecurity’s Internal Network Penetration Testing services—a strategic defense against threats that may lurk within your organization’s digital boundaries.


Sophisticated Internal Approach
Internal Compromise and Insider Threat Simulation
Detailed Manual Approach
Active Directory Assessment
Strafe’s Internal Penetration Testing includes a thorough assessment of your Active Directory environment. This critical component of your internal infrastructure is meticulously examined for vulnerabilities, ensuring that the backbone of your network is secure against potential compromise and unauthorized access.
Advanced Attack Scenarios
Going beyond identification, our engineers simulate advanced attack scenarios tailored to your organization. These scenarios may include complex attack vectors, sophisticated and custom malware simulations, or other relevant threats. This proactive approach allows us to understand potential attack pathways and assess the extent of potential damage. The advanced approach assists in identifying whether or not Endpoint Detection and Response (EDR) services can identify advanced techniques.
Organizations with an online presence need a team of experts to give them the peace of mind to continue growing and excelling. We are confident that Strafe Cyber is the best option for you.
- Expertise and Experience
- Cutting-Edge Technology
- Customized Testing Methodologies
- Advanced Threat Emulation
